Call for Board Member Nominations
01 Jan 2024
We are open to nominations for new people to join the Open Privacy Research Society’s Board of Directors!
In particular, we are looking for individuals who have experience in fundraising and organizational capacity building. But if you think you have a skill you can bring to the Open Privacy board then we really want to hear from you.
Read More
2022 End Of Year Report
28 Nov 2023
Discreet Log: July 2023!
14 Jul 2023
Welcome to Discreet Log for July 2023!
Discreet Log is our regular digest providing a summary of the research, projects and tools that we work on at Open Privacy.
In this edition we want to tell you about the release of Cwtch Beta 1.12, new updates to Repliqate, and an update on our 2023 fundraising goal.
Read More
Discreet Log: April 2023!
04 May 2023
Welcome to Discreet Log for April 2023!
Discreet Log is our monthly digest providing a summary of the research, projects and tools that we work on at Open Privacy.
In this edition we want to tell you about how to test new features in Cwtch Nightlies, and introduce you to the new Cwtch developer documentation!
Read More
Discreet Log: March 2023!
04 Apr 2023
Welcome to Discreet Log for March 2023!
Discreet Log is our monthly digest providing a summary of the research, projects and tools that we work on at Open Privacy.
In this edition we want to tell you about all the exciting new Cwtch Development Logs that have been released this month - including the Cwtch Beta 1.11 release, and updates on the Cwtch Stable roadmap, new volunteer documentation, and more!
Read More
Discreet Log: February 2023!
28 Feb 2023
Welcome to Discreet Log for February 2023!
Discreet Log is our monthly digest providing a summary of the research, projects and tools that we work on at Open Privacy.
In this edition we want to tell you about all the exciting new Cwtch Development Logs that have been released this month - including news of UI Testings, and updates on reproducibility, and automation, of Cwtch bindings!
Read More
Discreet Log: January 2023!
31 Jan 2023
Welcome to Discreet Log for January 2023!
Discreet Log is our monthly digest providing a summary of the research, projects and tools that we work on at Open Privacy.
In this edition we want to tell you about all the exciting new Cwtch Development Logs that have been released this month - including news of Cwtch Stable and Reproducible Builds! -and how to follow Cwtch updates across social media.
Read More
Discreet Log #35: Cwtch 1.10 Released!
16 Dec 2022
Welcome to Discreet Log 35! A regular update providing a look into the research, projects and tools that we work on at Open Privacy. This edition we want to tell you about all the exciting new features in Cwtch 1.10.
Read More
Discreet Log #34: Scaling Cwtch Connections
15 Nov 2022
Welcome to Discreet Log 34! A regular update providing a look into the research, projects and tools that we work on at Open Privacy. This edition we want to tell you about some upcoming changes to connection management for Cwtch 1.10, the ongoing Cwtch Bug Bash list, updated build containers, and a new article about P2P communications featuring Cwtch!
Read More
Discreet Log #33: Cwtch 1.9 Released! Privacy is Consent T-shirts have been shipped!
16 Sep 2022
Welcome to Discreet Log 33! A regular update providing a look into the research, projects and tools that we work on at Open Privacy. This edition we want to tell you about all the exciting new features in Cwtch 1.9, Privacy is Consent t-shirts, and some recent reporting of vulnerabilities in the email client Thunderbird.
Read More
2021 End Of Year Report
01 Aug 2022
Discreet Log #32: Cwtch Documentation
03 Jun 2022
Welcome to Discreet Log 32!
This week we want to tell you exciting information about the new Cwtch Handbook; and a video and comments from a recent panel on Privacy and Human Rights featuring Dan Ballard, our Director of Engineering.
Please consider donating or volunteering to help us continue our research and development of surveillance resistant software.
Read More
Discreet Log #31: Privacy is Consent
20 May 2022
Welcome to Discreet Log 31!
We are well into Open Privacy’s 2022 fundraising drive! We’ve gotten some wonderful new supporters, but currently not enough to support all our staff continuing on through the year. We’re still looking at how we can keep pursuing our goals with reduced capacity.
Please consider donating or volunteering to help us continue our research and development of surveillance resistant software.
Read More
Discreet Log #30: Future Plans for Cwtch
04 May 2022
We have kicked off Open Privacy’s 2022 fundraising drive! We’ve gotten some wonderful new supporters, but currently not enough to support all our staff continuing on through the year. We’re still looking at how we can keep pursuing our goals with reduced capacity.
Please consider donating or volunteering to help us continue our research and development of surveillance resistant software.
Read More
Discreet Log #29: Cwtch 1.7 and Update Bot!
22 Apr 2022
We have kicked off Open Privacy’s 2022 fundraising drive! We’ve gotten some wonderful new supporters, but currently not enough to support all our staff continuing on through the year. We’re still looking at how we can keep pursuing our goals with reduced capacity.
Please consider donating or volunteering to help us continue our research and development of surveillance resistant software.
Read More
Discreet Log #28: Message Text Formatting
08 Apr 2022
We have kicked off Open Privacy’s 2022 fundraising drive! We’ve gotten some wonderful new supporters, but currently not enough to support all our staff continuing on through the year. We’re still looking at how we can keep pursuing our goals with reduced capacity.
Please consider donating or volunteering to help us continue our research and development of surveillance resistant software.
Read More
Discreet Log #27: Cwtch Android Improvements
25 Mar 2022
We have kicked off Open Privacy’s 2022 fundraising drive! We’ve gotten some wonderful new supporters, but currently not enough to support all our staff continuing on through the year. We’re still looking at how we can keep pursuing our goals with reduced capacity.
Please consider donating or volunteering to help us continue our research and development of surveillance resistant software.
Read More
Discreet Log #26: Cwtch Translations and Donate Bitcoin via BTCPay
10 Mar 2022
We have kicked off Open Privacy’s 2022 fundraising drive! We’ve gotten some wonderful new supporters, but currently not enough to support all our staff continuing on through the year. We’re still looking at how we can keep pursuing our goals with reduced capacity.
Please consider donating or volunteering to help us continue our research and development of surveillance resistant software.
Read More
Discreet Log #25: Notifications, Cwtch 1.6.1, Fundraising
25 Feb 2022
We have kicked off Open Privacy’s 2022 fundraising drive! We’ve gotten some wonderful new supporters, but currently not enough to support all our staff continuing on through the year. We’re starting to look at how we can keep pursuing our goals with reduced capacity.
As such, we will be changing the format of Discreet Log to lighten the writing load on staff and as a reflection of reduced development speed and capacity going forward.
Read More
Discreet Log #24: 4 Years of Open Privacy! Cwtch 1.6! We need your Support!
11 Feb 2022
Four years ago today, on February 11th 2018, we officially incorporated the Open Privacy Research Society.
The work that we do couldn’t exist without an active and amazing base of supporters, like you, who enable our mission - researching and developing privacy enhancing technologies focused on those people and communities that need them most.
To celebrate our 4th year anniversary I would like to invite you to review the amazing work that you helped support over the last few years - and once again ask for your help and support to help us continue our mission in 2022.
Read More
Discreet Log #23: Improving Cwtch testing using Cucumber/Gherkin scripts
28 Jan 2022
As a small team producing a complex application, automated testing is an important part of the Cwtch development process, providing confidence that new features or fixes aren’t breaking old ones that we may not always think to test manually. In previous posts, we’ve talked about how we use widget testing, integration testing of the Cwtch backend library, and fuzzing to accomplish this. What we’ve been lacking to date, however, is a wide-ranging (feature complete) frontend integration test. This week’s Discreet Log will talk about how we’re accomplishing that alongside the 1.6 release using Gherkin scripting.
Read More
Discreet Log #22: Building on Cwtch - A Vision for 2022
10 Dec 2021
This week we have been putting the finishing touches on Cwtch Beta 1.5, a much larger release than its predecessors due to the new features and significant refactors that have been planned in.
I wanted to take a moment away from pull requests and fuzz testing to talk to you about the future of Cwtch and present to you a vision for the future of surveillance resistant applications. Don’t worry, there isn’t a single blockchain or NFT in sight!
Read More
Discreet Log #21: Coming Soon: Image Previews and Links!
26 Nov 2021
Cwtch Beta 1.5, slated for release in mid-December, includes a number of quality-of-life improvements that users have been asking for. Some are even already available in nightlies, such as the clickable links experiment. This post will give you a small preview of what’s coming and, in Discreet Log tradition, talk about some of the technical choices we made and try to answer questions you might have about the implementation.
Read More
Discreet Log #20: Cwtch Servers Experiment
11 Nov 2021
Our 1.4 Release of Cwtch now includes a new experiment: hosting and management of Cwtch Servers inside the Cwtch app.
What are Cwtch Servers and What are They For?
Traditionally messengers have solved offline delivery with centralized servers which, as a side effect, must collect metadata to operate. In a step towards decentralization some federated services like Mastodon or Matrix, do technically allow anyone to run their own server, but the setup is usually a barrier to everyone doing it, and still results in metadata collection by the service operator.
Directly messaging a contact in Cwtch is done peer to peer over Tor v3 onion servers. This is optimal as there are no intermediary services used. However, this comes with a major constraint: both parties must be online. If we want offline message delivery, we need some form of shared infrastructure to support it.
Cwtch servers are designed to be untrusted. Which means that don’t learn anything about the messages they are hosing or the profiles or groups those messages are associated with.
Cwtch servers can be hosted privately, for efficient, small group communication, or shared publicly to allow people without the resources access to private, shared, infrastructure.
Read More
Discreet Log #19: Cwtch Roadmap (1.4 to 1.7)
29 Oct 2021
Early last week the Open Privacy Executive Team met up to work in person for the first time since the start of the pandemic. On the agenda was organizational planning, Cwtch development and building out a new roadmap.
For this week’s Discreet Log, I would like to present an overview of our plans for the next 6 months and invite you to help us support further development on truly decentralized and surveillance resistant technology.
Read More
Discreet Log #18: libCwtch in Rust
12 Oct 2021
LibCwtch is our interface (API) library to Cwtch, which was started over 3 years ago as a Go language project. Since then we have started using Flutter and Dart to build our front end UI which meant we needed a more language agnostic interface to Cwtch so we created libCwtch, which is some wrapper functionality around Cwtch and it compiles to a C library that any language can access via FFI. The first language binding we made for libCwtch was Dart which is currently built into our cwtch-ui. At some point we’d like to find the time to break the Dart bindings out into a standalone Dart package that anyone can use to access libCwtch from Flutter/Dart.
Since starting work with Go 3 years ago our interest in working in Rust has been growing so it was the logical next language we would look at to create bindings for.
Read More
Discreet Log #17: Filesharing FAQ
01 Oct 2021
Welcome to Discreet Log! A fortnightly technical development blog to provide an in-depth look into the research, projects and tools that we work on at Open Privacy. For our 17th edition Erinn Atwater answers some questions about the new filesharing feature in Cwtch 1.3.
Today’s release of Cwtch 1.3 includes support for a new experimental feature: file sharing! Windows, Mac, Linux and Android users can enable the File Sharing experiment from the global settings panel. Files are sent peer-to-peer directly over Cwtch/tor connections. In this week’s Discreet Log, I thought I’d answer some questions about the finer points of how it all works.
Read More
Discreet Log #16: Cwtch Secure Development Handbook
17 Sep 2021
Welcome to Discreet Log! A fortnightly technical development blog to provide an in-depth look into the research, projects and tools that we work on at Open Privacy. For our 16th edition Sarah Jamie Lewis talks about recent updates to the Cwtch Secure Development Handbook.
Over the years Cwtch has evolved from a single codebase proof-of-concept to an ecosystem that spans several subcomponents, historical and current UI front-ends, platform-specific code and multiple language bindings (more on that in a few weeks).
Keeping track of the privacy and security risks, mitigations and concerns in addition to all the other complexity is a job that is too big for any one codebase, issue tracker or wiki. That is why, a few years ago, I started maintaining the Cwtch Secure Development Handbook.
Recently the handbook has undergone a few updates, and that is what I want to talk about this week.
Read More
Discreet Log #15: Cwtch Comes to MacOS
03 Sep 2021
Open Privacy just released Cwtch Beta 1.2 and one of the biggest new features was an full new MacOS port.
Read More2020 Financial Statements - Notice to the Reader
25 Aug 2021
2020 End Of Year Report
25 Aug 2021
2020 End Of Year Report
Discreet Log #14: Lockbox Case Study
19 Aug 2021
Fighting back against tech abuse and surveillance is (unfortunately) an ever-ongoing job, and every once in a while our developers need to come up from the privacy mines to take some much-needed R&R. While Erinn is on staycation (traveling the cyberverse to sample the latest cryptodelicacies and witness hot new mathematical attractions), we thought we’d share with you a recent case study we wrote following last year’s engagement creating the Lockbox encrypted form app to power a local mutual aid fund that arose out of the COVID pandemic.
Read More
Discreet Log #13: Metadata Resistant File Sharing
04 Aug 2021
The ability to send images, audio and other files is one of the most requested Cwtch features, and with the Beta now released the Cwtch team have recently started discussing how to support safe and secure metadata resistant file sharing.
This is by no means an easy problem. In this log entry I will discuss some open problems, provide some insight into the design work currently unfolding, and finish up with a sketch roadmap for getting these features into Cwtch.
Read More
Discreet Log #12: Native Porting
21 Jul 2021
We released Cwtch 1.1 last week, our first Beta update, with a ton of bug fixes and even a few new features and the two reasons we’ve been able to move this fast even with such a small team are both the maturity of Cwtch now as a platform, but also, because Flutter has been working well as a cross-platform framework with quality high level widgets that let us build the UI rapidly. That said, Flutter having good cross-platform widgets doesn’t mean it’s seamless frictionless work to bring it to 3 platforms, especially when support for the Desktop ones are still very new to Flutter.
We’ve already blogged about building Android service support into the Cwtch Flutter app as one big and ongoing example of that work. Additionally, each platform handles notifications differently, and so on Android our notification work overlaps with our service support work, as reported above. Today I wanted to take a look at some other platform specific work we’ve done for Windows and Linux.
Read More
Discreet Log #11: Integrating FFI processes with Android services
09 Jul 2021
In Discreet Log #9, Dan talked about how we use FFI to connect our Flutter frontend to our Go backend Cwtch library on both desktop and Android platforms. In the leadup to the release of the Cwtch Beta last week, we finished the Android service work mentioned in that post and are going to go over how it works in this week’s edition of Discreet Log!
Read More
Discreet Log #10: Cwtch Beta and Beyond
25 Jun 2021
Today I am so proud to be announcing the official start of the Cwtch Beta series of releases with support for Windows, Linux and Android devices.
Release builds are now available to download from cwtch.im, and will soon be available from the Google Android Playstore.
Read More
Discreet Log #9: Flutter with Native Go Libraries
09 Jun 2021
Why
Languages, programming environments, and frameworks are all good for different things. When we started Cwtch we evaluated Go as a good candidate for building a system library. In our ongoing research we’ve also identified Rust as having excelent properties for making very safe critical apps. However neither of these langauges come equiped with frameworks for rapidly, easily and seamlessly building crossplatform UIs. If you find yourself in a similar situation starting out, or in a situation where there is a mature solution to a problem in a language that is also not well suited to UI building than you might find this overview of our work combinging a robust Go networking library, Cwtch, with Flutter to build a single UI and codebase for Windows, Android, and Linux.
Read More
Discreet Log #8: Notes on the Cwtch Chat API
28 May 2021
We envision Cwtch as a platform for providing an authenticated transport layer to higher-level applications. Developers are free to make their own choices about what application layer protocols to use, whether they want bespoke binary message formats or just want to throw an HTTP library on top and call it a day. Cwtch can generate new keypairs for you (which become onion addresses; no need for any DNS registrations!) and you can REST assured (hehe) that any data your application receives from the (anonymous communication) network has been authenticated already.
For our flagship titular Cwtch Messenger app, we wanted an application layer message protocol that is lightweight/compact, and common enough that we can easily re-parse raw messages from a variety of frontends whenever the need arises.
Read More
Discreet Log #7: UI Security Testing with Fuzzbot
14 May 2021
The user interface remains the largest and riskiest part of the Cwtch system. While we can (and do) strictly scope the code involved in the Cwtch protocol, we are at the mercy of large UI frameworks when it comes to displaying and interacting with the protocol in a way that is usable and cross-platform.
We can’t vet every single line of code in UI frameworks, and even if we did these frameworks often produce intermediate code during their compilation (e.g. to generate specific code that will work on Window, Linux, iOS or Android) which in turn invokes dynamic libraries that exist on those systems with their own security concerns and considerations.
Fuzz testing allows us to battle harden Cwtch against possible failure cases in a way that is efficient and scalable, and for that we have Fuzz Bot!
Read More
Discreet Log #6: A Tour of the Cwtch Integration Test
30 Apr 2021
I talked previously on how we had built our automated build and test system and the benefits in quality that gave us. Today I’d like to zoom in to one of my favourite pieces of our quality assurance infrastructure, the Cwtch integration test. This test is important because we’ve written it to hit as much of the Cwtch code base as possible and test it works in one go. It also sits on top of several other crucial components and thus gives them extra coverage and workout too, such as Tapir and our Connectivity package.
Read More
Discreet Log #5: Improving Safety with Cwtch UI Tests
16 Apr 2021
In my last post, I discussed porting Cwtch’s user interface from Qt to Flutter (using our common Go backend).
This week, I’m going to give an introduction of our use of flutter testing tools to improve the quality and safety of the new Cwtch UI.
We will take a look at Flutter widget and integration tests, and how we are using them to test everything from our custom textfields to safety critical features like “does blocking actually work?”.
Read More
Discreet Log #4: On Tapir, Rust, and notes for building future anonymous applications.
02 Apr 2021
Cwtch is still experimental software, and we have plenty of open questions about turning it into an application that meets our increasingly higher standards for anonymity, privacy and consent. It is no small feat and requires constantly evaluating our assumptions and previous expectations.
As we finally approach a Cwtch Beta, I want to take the opportunity to look back, with hindsight and fresh eyes, in order to understand where we go next.
Read More
Discreet Log #3: A brief history of Open Privacy automated build systems, and our recent build system upgrade
19 Mar 2021
A Brief History of Open Privacy Automated Build Systems
I’ve had a few experiences with build systems over my career. After joining a small startup, I was horrified to find that their deployment ‘process’ for 6 micro-services, entailed devs logging into each of the two servers they initially had for production, and manually checking out the latest code, rebuilding it, and restarting it. I spent some of my early time there building an automated build system with Jenkins.
Later, I worked at a large tech company which had a pretty decent and robust system that had been developed in-house. Sadly, even in that company, operational excellence levels varied quite wildly from team to team. Some teams had full Continuous Integration (CI), which is a fully automated build pipeline deploying code that passes the tests to production automatically, which speaks highly of the team trusting their tests to catch any and all issues. Meanwhile, many other teams not only had manual approval steps in their build pipelines but many of those approvals were attached to very long documents of required manual testing steps.
Read More
Discreet Log #2: Qwtch to Flwtch: Porting Cwtch's Go/Qt Frontend to Go/Flutter
05 Mar 2021
Welcome to Discreet Log! A fortnightly technical development blog to provide an in-depth look into the research, projects and tools that we work on at Open Privacy. For our second post Erinn Atwater documents the development of a new Flutter-based UI for Cwtch.
The Cwtch library provides a backend written in Go intended to provide support to a number of other apps we have planned that use Cwtch connections as a (metadata-minimizing, authenticated) transport layer. Sarah has been working on Tapir so the backend has an open path forward in Rust, but today we’re here to chat about the other side!
Read More
Discreet Log #1: Anonymity, Bandwidth and Fuzzytags.
19 Feb 2021
Welcome to Discreet Log! A fortnightly technical development blog to provide an in-depth look into the research, projects and tools that we work on at Open Privacy. For our first post Sarah Jamie Lewis will take us through her investigations into some new research on “fuzzy message detection” schemes that might hold the key to bandwidth efficient metadata resistant offline messaging in Cwtch…
Anonymous messaging systems (and other privacy-preserving applications) often require a mechanism for one party to learn that another party has messaged them.
Many schemes rely on a bandwidth-intensive “download everything and attempt-decryption” approach. Others rely on a trusted 3rd party, or non-collusion assumptions, to provide a “private” service.
It would be awesome if we could get an untrusted, adversarial server to do some of that work for us without compromising metadata-resistance.
Read More
3 Years of Open Privacy
11 Feb 2021
Three years ago, on February 11th 2018, we officially incorporated the Open Privacy Research Society. At that point in time I don’t think any of us had any idea how the following years would go.
2020 was difficult and challenging. The work outlined here is a fraction of what we had hoped to achieve. 2020 impacted our projects, our priorities, and our lives. That said, I think it represents some of the most important work we have done so far, and I am excited to push it as far as we can in 2021.
This work couldn’t exist without an active and amazing base of supporters, like you, who enable our mission - researching and developing privacy enhancing technologies focused on those people and communities that need them most.
To celebrate our 3rd year anniversary I would like to invite you to review some of the amazing work that you helped support in 2020 - and once again ask for your help and support to help us continue our mission in 2021.
Read More2019 Financial Statements - Notice to the Reader
01 Aug 2020
2019 End Of Year Report
01 Aug 2020

2019 End Of Year Report

Release: Lockbox encrypted web forms
14 Apr 2020
Today we are releasing the first cut of Lockbox, an application for creating simple encrypted web forms!
Read More
2 Years of Open Privacy
11 Feb 2020
Two years ago, on February 11th 2018, we officially incorporated the Open Privacy Research Society. Since then we’ve grown so much as an organization. We now have 8 board members, and 4 staff members, multiple open source projects, an office and, most importantly, an active and amazing base of supporters who enable us to do our important work - researching and developing privacy enhancing technologies focused on those people and communities that need them most.
To celebrate our 2nd year anniversary I would like to invite you to review some of the amazing work that you helped support in 2019 - and once again ask for your help and support to help us continue our mission in 2020.
Read More
Welcoming Marcia as our new Staff Designer
13 Jan 2020
Late last year we set out to find a new Staff Designer to work with us to set the direction of the look and feel of our software projects and websites.
We received many fantastic applications, and we are very excited to announce that we have now hired a Staff Designer!
Read More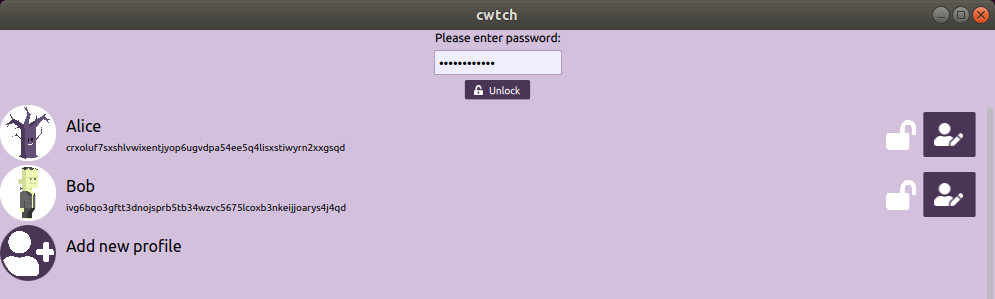
Cwtch Alpha 0.3.1
17 Dec 2019
Today we are proud to announce and release Cwtch Alpha 0.3.1! Featuring a first cut of profile management.
Read More
Incentivizing Trustlessness
03 Dec 2019
We are delighted to announce that the Zcash Foundation donated 1044.41369 ZEC (or $40,000 USD at time of donation) to the Open Privacy Research Society. We would like to send a big Thank You to the Zcash Foundation for their support!
While the donation was unrestricted, we would also like to take this opportunity to announce a number of new initiatives (some involving zcash!) that this funding will contribute to!
Read More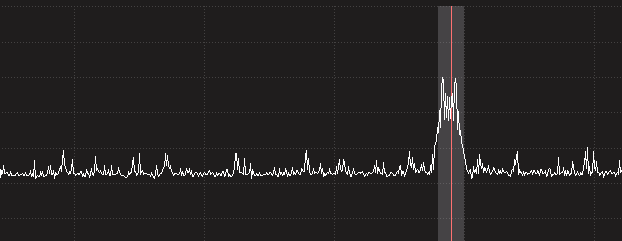
Press Release: Vancouver Coastal Health Stops Broadcasting Patient Diagnosis
26 Sep 2019
Vancouver, BC - The Open Privacy Research Society has received an update from Vancouver Coastal Health (VCH) after last weeks Press Release publicly disclosing that we had discovered that the sensitive medical information of patients being admitted to certain hospitals across the Greater Vancouver Area is being broadcast, unencrypted, by hospital paging systems, and that these broadcasts are trivially interceptable by anyone in the Greater Vancouver Area.
Read More2018 Financial Statements - Notice to the Reader
24 Sep 2019
2018 End Of Year Report
24 Sep 2019

Releasing Our 2018 Financial Statements & End of Year Report
24 Sep 2019
Open Privacy was founded on the belief that the world can be better. We started as a group of researchers and technologists who were frustrated by the ever growing stranglehold of surveillance capitalism and the harm it was causing marginalized and at-risk communities. We wanted to build an organization that served those that mainstream groups ignore: sex workers, queer people, those impacted by intimate parter or family abuse, and human rights activists, to name just a few.
Read More
Cwtch Alpha 0.3.0
23 Sep 2019
Today we are proud to announce and release Cwtch Alpha 0.3.0 and kick off the 0.3 alpha release cycle! This release line is the first where the Android experience is now expected to work reliably alongside the desktop versions (Windows and Linux). This is the culmination of a lot of work over the past 5 months.
Read More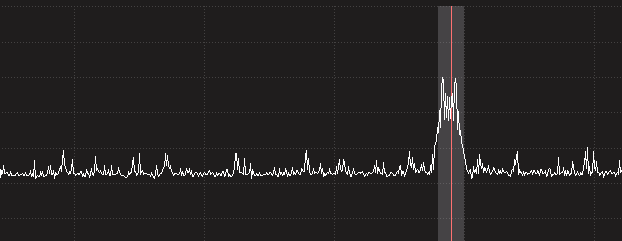
Press Release: Open Privacy discovers unencrypted patient medical information broadcast across Vancouver
09 Sep 2019
Vancouver, BC - The Open Privacy Research Society has discovered that the sensitive medical information of patients being admitted to certain hospitals across the Greater Vancouver Area is being broadcast, unencrypted, by hospital paging systems, and that these broadcasts are trivially interceptable by anyone in the Greater Vancouver Area.
Read More
Cwtch Alpha 0.2.0
19 Aug 2019
Today we are proud to announce and release Cwtch Alpha 0.2.0 and kick off the 0.2 alpha release cycle! Some big improvements have landed since 0.1.5 both on the frontend and the backend side of things and we’ve very excited about this release! We’ll go over the changes and then talk about some of what is planned for the 0.2 cycle.
Read More
Speak Math To Power: Get Your Limited Edition Commemorative T-shirt
06 Aug 2019
In March this year Sarah Jamie Lewis of the Open Privacy Research Society, along with Vanessa Teague (University of Melbourne), and Olivier Pereira (UCLouvain) published details of critical vulnerabilities impacting evoting systems in Switzerland and Australia. These vulnerabilities were soon confirmed by the vendor Scytl, resulting in an emergency patch being installed during an election in New South Wales, and a “temporary” suspension of evoting offerings by Swiss Post.
In June the Swiss Federal Council, citing these disclosures, delayed the introduction and evoting as an official option, and shortly after SwissPost announced that it would not be offering its system for use in the October federal elections (despite having offered it in previous elections).
Just as math can protect the speech of the marginalized from the powerful, it can also be used to prove to everyone that power is not working as it claims.
Speaking math to power works.
Read More
Cwtch Alpha 0.1.5
26 Jul 2019
Today we are pleased to release Cwtch Alpha 0.1.5. Changes in this new release include:
- A progress spinner in the UI for groups indicating when they are connected but syncing with the server
- Chat text bar is locked until a peer to peer connection is established, or a group is synced
- Minor improvements in “performance” in that we removed a few threads that poll for events and replaced them with events and event handlers
Cwtch Alpha 0.1.4
22 Apr 2019
Today we are pleased to release Cwtch Alpha 0.1.4. Changes in this new release include:
- Lots of UI scaling fixes that should make it more consistent and better across many displays, especially mobile
- Beginnings of Android notifications
- Big speedups to group loading (most noticeable on Android)
- Version and build date in settings
Cwtch Alpha 0.1.3
26 Mar 2019
Today we are pleased to release Cwtch Alpha 0.1.3. Changes in this new release include:
- Translations support!
- Portuguese, German and French translations
- Android save user name fix
- Splash screen where needed (mostly android)
- Group membership pane
Cwtch Alpha 0.1.2
04 Mar 2019
We announced the Cwtch Alpha 2 weeks ago. Since then we’ve seen many people trying Cwtch out in different ways, from building it themselves to running the supplied binaries. From this we’ve received lots of feedback in our issue tracking system. We also started using Cwtch (dog fooding) ourselves for some dev team communication.
Today we are releasing a new Cwtch alpha update, 0.1.2 that contains the following work and more:
Read More
Board Member Spotlight: Norman Shamas
19 Feb 2019
Over the next few weeks we will be telling many of the stories of the first year of Open Privacy through releases, articles, blog posts, board member spotlights and interviews. We will also be laying out ambitious goals for the next year. Today we hear from Norman Shamas about why they are involved in Open Privacy.
Read More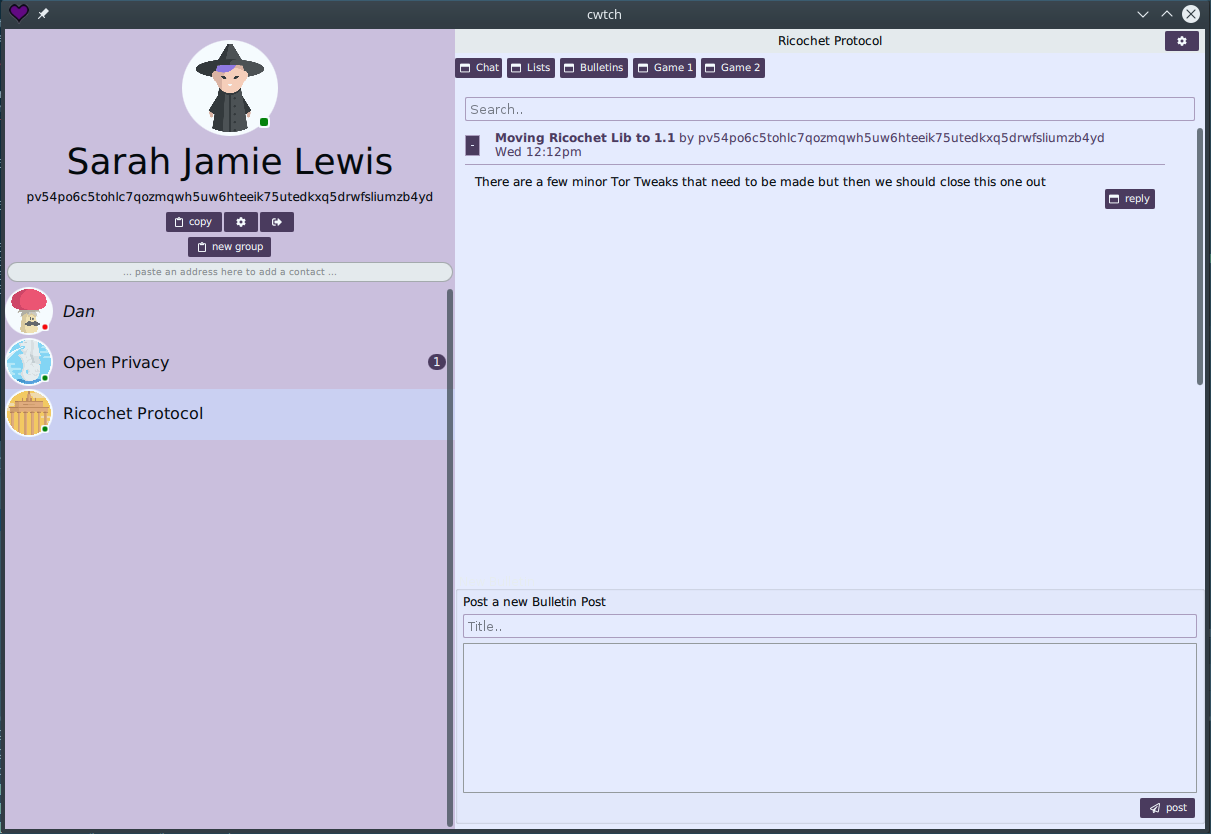
Happy Valentine's Day: Announcing Cwtch Alpha, A Start to Building Consensual Applications
14 Feb 2019
Cwtch is a Welsh word roughly translating to “a hug that creates a safe place”. Cwtch is also our decentralized, privacy-preserving, asynchronous multi-party messaging protocol that can be used to build consensual applications.
What better day to launch the alpha of a project designed to bring people together safely and securely than on Valentine’s day?
Read More
One Year of Open Privacy
11 Feb 2019
Open Privacy started as a group of researchers and technologists who were frustrated by the ever growing stranglehold of surveillance capitalism and the harm it was causing marginalized and at-risk communities. We wanted to build an organization that served those that mainstream groups ignore: sex workers, queer people, those impacted by intimate parter or family abuse, and human rights activists (to name just a few).
Read More
Open Infrastructure at Open Privacy
05 Oct 2018
Open Privacy believes in using and producing open source solutions and open infrastructure. Many values contribute to our belief and mandate for open solutions including preferring ownership to rent, preferring customizability and control, and desiring to share our work and results with the world. This post describes our process for building our infrastructure in the first half year of starting out as a nascent non-profit.
Read More
Announcing Cwtch: Privacy Preserving Infrastructure for Asynchronous, Decentralized, Multi-Party, and Metadata Resistant Applications
28 Jun 2018
Open Privacy believes in empowering users in ways that enable consent to and control over the movement of their data. The ebb and flow of current communication technologies has created a situation in which users are forced to either relinquish control over their personal information to dozens of unknown companies and government agencies, or sit on the sidelines and refrain from participating in culture and public society. Worse, many tools collect information on us that can be used against us in ways that are difficult to understand or predict. Nowhere is this impact felt harder than in the marginalized communities which Open Privacy exists to serve. We see only one solution to this problem: taking our data back into our own hands, and removing the ability of service providers to see our data at all. Today we announce the first step on this long journey: Cwtch.
Cwtch (a Welsh word roughly translating to “a hug that creates a safe place”) is a decentralized, privacy-preserving, asynchronous multi-party messaging protocol that can be used to build metadata resistant applications.
Read More
Open Privacy filed an intervention with the CRTC opposing FairPlay
09 Apr 2018
Recently we filed an intervention with the CRTC opposing the Fairplay website-blocking proposal. We believe that the CRTC’s acceptance of this proposal would pose a dire threat to Canadian Internet users’ privacy and access to information. In this post we break down our intervention and explain why we filed it, and why we believe there is much more to be done.
Read More
Press Release: Open Privacy Calls On CRTC To Adopt Manila Principles
04 Apr 2018
OPEN PRIVACY CALLS ON CRTC TO ADOPT MANILA PRINCIPLES
Vancouver, BC — Open Privacy Research Society, a new Canadian not-for-profit group based in Vancouver, has filed an intervention in the CRTC’s hearing on ISP-blocking application by urging the CRTC to endorse the Manila Principles on Intermediary Liability.
The Manila Principles are an international charter. They set out principles to help ensure efforts to involve intermediaries, like ISPs, in the content they carry – like requiring them to create kill switches to block some content – respect users’ rights, including freedom of expression and the right to privacy.
Read More
Announcing Open Privacy Research Society
28 Mar 2018
Privacy is Consent. Privacy is the right to consent. Privacy is the right to withdraw consent.
The Open Privacy Research Society (Open Privacy for short) is a non-profit Canadian group based in Vancouver, British Columbia. We believe that moral systems enable consent. Our society exists to invent, create, build, test, deploy, promote, and to encourage the development of such systems.
Read More